Advance Keylogger Software

Advance Key logger is useful to keep track of system and internet activities performed on your PC while you are away. Powerful utility easily records keyboard typed key activities, voice chat conversations, clipboard contents, system sound activities, time setting modifications, system startup time etc at regular interval of time. Key logger runs in stealth mode and is helpful for the Companies, at Home, Cyber Cafés etc to monitor business (employees), for parental monitoring to monitor the child activities etc without even mattering that how far you are from your computer system.
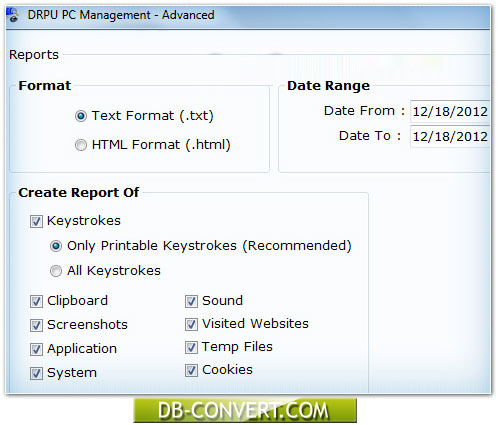
Surveillance utility secretly captures Windows screenshots at regular time interval with the slide show facility so that you can easily know the order of the applications accessed by the users. Software provides detailed report of all recorded activities by sending log file via email at user defined email id or uploading log file using FTP Server settings.